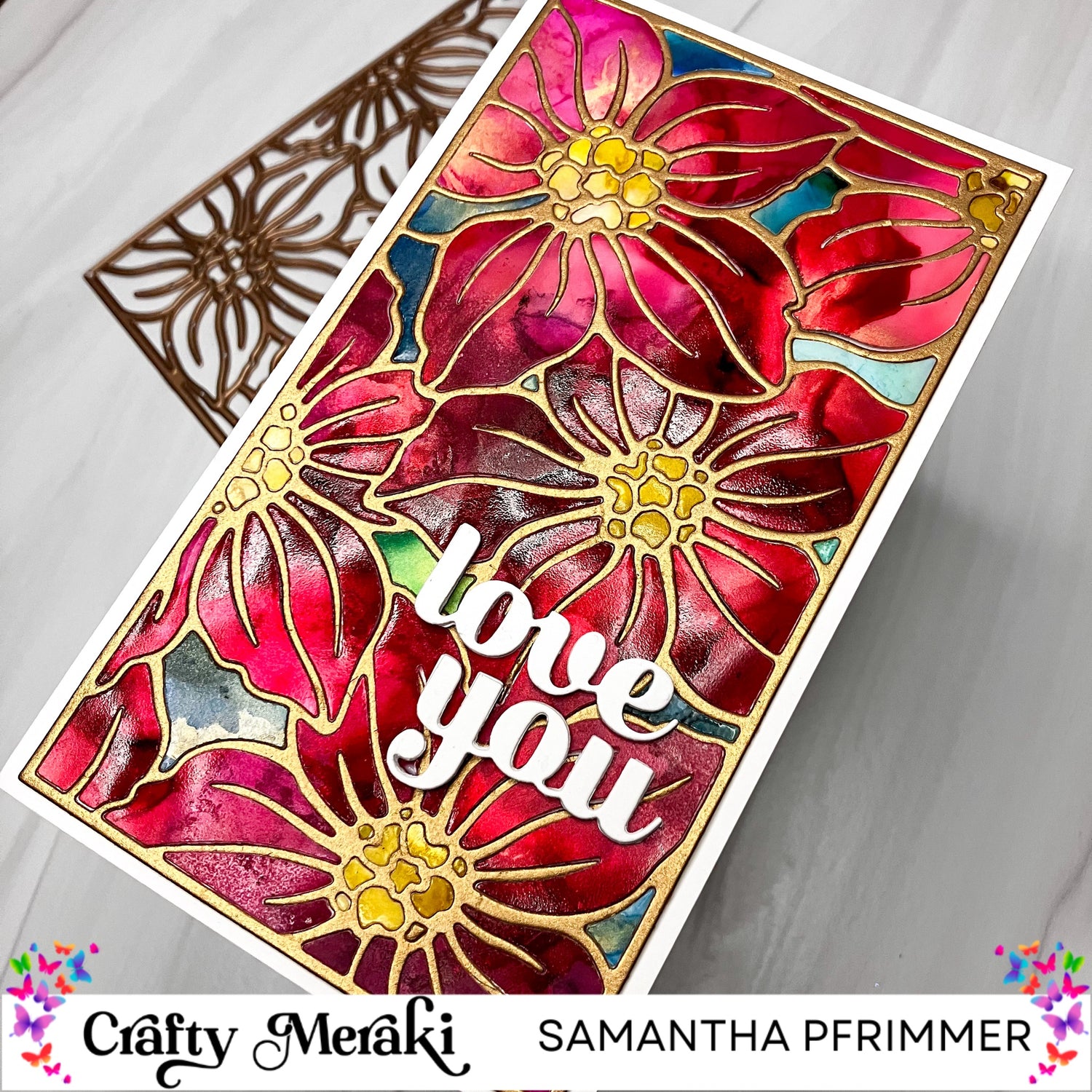
Hi everyone! Samantha here. I am so excited to be the February Guest Designer for Crafty Meraki. This week the focus is on die-cutting, and I thought it would be fun to share my technique for creating a "stained glass window" card using alcohol inks and the beautiful Lenten Rose Mini Slimline Para-Die.

To start my project I grabbed drinking straws, alcohol ink card stock, Ranger alcohol inks, and some 91% rubbing alcohol.
I needed three sheets of cardstock for my card, one each in shades of red, yellow, and blue. To create each paper, I added various shades of inks along with Gold and Snow Cap Mixatives and created swirling patterns by blowing through a straw. I also added in rubbing alcohol to help move the colors around the paper. Once done, I let them fully dry overnight before spraying each sheet with a few layers of Kamar Varnish to seal in the color.

Next, it was time to die cut.
I cut each sheet of cardstock using the Lenten Rose Para-die. I very carefully, tried to keep all of the die cuts pressed within the die itself before applying them to a sheet of Press 'N Seal wrap. My goal was to keep the die cuts together in the shape of the cover plate die for ease when inlaying the die cuts later on.

After cutting my alcohol ink-friendly cardstock , I cut a frame with the Lenten Rose Para-die out of brushed gold cardstock and adhered it to a 3.5" x 6.25" white card panel as my base for the inlay work.
To do the actual inlay, using tweezers and a pick-up tool, I carefully grabbed each die cut piece from my Press 'N Seal sheets and glued them in place matching the die cut to its corresponding spot on the frame. I used the red for the petals, the gold for the flower centers, and the teal blues for the areas between the flowers.

Once my panel was complete, I added a white "Love You" sentiment using a die from my stash as well as giving the panel a white border. I cut a card base 7.5" x 6.5" scoring at the 3.75" mark and then glued down my inlay card panel.
This card took some time to complete. A little more than I was expecting, but I just love the uniue results. I hope you give it a try!



52 comments
Blizzyeverhard
3981 Moore St APT 101, Los Angeles, CA 90066
to help me get my money back
Many binary operations are rippers. I invested about $420,000 then I decided to withdraw after several weeks but the withdrawal wasn’t successful, then I tried to contact the binary operation email and phone number, I didn’t get any response from them that was when everything started looking weird. Some weeks later I got a mail from them insisting I should invest more money if I want to withdraw my money which I rejected, and I never heard from them again that it was when I knew I had been scammed. I was really devastated at that moment and felt so bad that my hard earned money was gone. After some month I came across a lot of testimonies on many bitcoin site how E/mail, SMITHWHITEHACKSERVICE@GMAIL COM had helped many people recovered there stolen, scammed or duped money on bitcoin or any other form on digital currency. I contacted them and they promised to help me get my money back, asked me some personal details of the scammer which I provided. The result was amazing. I recovered all my stolen money back within 72 hours. I was so happy as I never believed I could get my money back. Thanks SMITHWHITE HACK SERVICE you restore Joy into my life after several pains I’m so indebted!!
INFORMATION <> SMITHWHITEHACKSERVICE@GMAIL COM
WHATSAPP + 1 559 508 2403
Marius Walter
I fell victim to a very convincing forex scam where the scammers presented professional-looking graphs, trading dashboards, and portfolios of people who appeared to be earning consistently. This made the investment seem legitimate and trustworthy.
As a result, I lost 1,497 SOL and 347,000 USDT. When withdrawals became impossible and excuses kept coming, I realized it was a scam.
I then contacted Morphohack Cyber Service, who carefully reviewed my case and transaction details. Thanks to their professionalism and expertise, they were able to successfully help me recover my funds. I contacted them via email (Morphohack@cyberservices.com)
I’m truly grateful for their support and would recommend Morphohack to anyone who has fallen victim to crypto or forex scams.
Marius Walter
I fell victim to a very convincing forex scam where the scammers presented professional-looking graphs, trading dashboards, and portfolios of people who appeared to be earning consistently. This made the investment seem legitimate and trustworthy.
As a result, I lost 1,497 SOL and 347,000 USDT. When withdrawals became impossible and excuses kept coming, I realized it was a scam.
I then contacted Morphohack Cyber Service, who carefully reviewed my case and transaction details. Thanks to their professionalism and expertise, they were able to successfully help me recover my funds. I contacted them via email (Morphohack@cyberservices.com)
I’m truly grateful for their support and would recommend Morphohack to anyone who has fallen victim to crypto or forex scams.
Marius Walter
I fell victim to a very convincing forex scam where the scammers presented professional-looking graphs, trading dashboards, and portfolios of people who appeared to be earning consistently. This made the investment seem legitimate and trustworthy.
As a result, I lost 1,497 SOL and 347,000 USDT. When withdrawals became impossible and excuses kept coming, I realized it was a scam.
I then contacted Morphohack Cyber Service, who carefully reviewed my case and transaction details. Thanks to their professionalism and expertise, they were able to successfully help me recover my funds. I contacted them via email (Morphohack@cyberservices.com)
I’m truly grateful for their support and would recommend Morphohack to anyone who has fallen victim to crypto or forex scams.
Alexhenry
18433 Wade Hill Rd, Patriot, IN 47038
TRUSTED RECOVERY SERVICEThe most well-known cryptocurrency in the world, Bitcoin, has become extremely popular in recent years. More people and companies are adopting Bitcoin and other cryptocurrencies as a form of investment due to their anarchic framework and high return potential. Nevertheless, the emergence of Bitcoin has also given rise to a number of security issues, resulting in instances of lost or unreachable Bitcoins. Consequently, there is an enormous increase in demand for expert Bitcoin recovery services. Ever felt like your heart sinks when you realise you can’t get to your Bitcoin? There is a bigger demand than ever for trustworthy Bitcoin recovery services due to the rising popularity of Bitcoin and other cryptocurrency. The security risks connected with Bitcoin are growing along with its value and use. There are several possibilities for consumers to lose access to their priceless digital assets, including device malfunctions, cyberattacks, and forgotten passwords and wallet seeds. smith white hack service can help in this situation. smith white hack service is the legitimate sidekick when it comes to obtaining your unidentified or unaccessible Bitcoins back. Years of experience and unmatched knowledge have allowed them to assist many people in regaining access to their digital assets. smith white hack service provides specialized solutions that increase your chances of getting your Bitcoins back by analyzing your particular circumstances and using cutting-edge recovery methods. I will suggest your urgent request for support from smith white hack services team through: Do not get left behind. Contact smith white hack service through Email:SMITHWHITEHACKSERVICE@GMAIL COM And also on WhatsApp +1 559 – 508 – 2403
Leave a comment
This site is protected by hCaptcha and the hCaptcha Privacy Policy and Terms of Service apply.